Hello fellow bug hunter!
I want to share some thoughts on a couple of changes I think could make the security process more transparent and beneficial for everyone — researchers, users, and browser vendors alike.
Microsoft is full of smart, well-intentioned people, and they have been making real progress on security. That said, two things I’d love to see adopted more broadly are:
- Patching vulnerabilities in 60 days or less, in line with the CERT disclosure policy of 45 days.
- Keeping a permanent reward system (aka bug bounty) open for their supported browsers.
That feels like a fair bar for today’s standards, and it’s actually even less than what others are doing in urgent cases. For reference, both Firefox and Chrome can ship security fixes within 24 hours when needed:
Firefox - […] should update automatically over the next 24 hours […]
Chrome - […] if we find an important security bug, we push out a fix within 24 hours—no update from you required.
The community has been vocal about wanting faster updates — the request “Allow Edge to be updated on its own” had 1715 votes, and Thurrott has written about it more than once. Reuters also covered the broader pattern:
The saga shows that Microsoft’s progress on security issues, as well as that of the software industry as a whole, remains uneven in an era when the stakes are growing dramatically.
Faster patching would benefit everyone, and I genuinely hope to see it happen.
And regarding bounties, both Google Chrome and Mozilla Firefox have clear rules about what counts as a bug and what doesn’t, to the point that Google publishes exactly what the reward is for each bug type (see Chrome and Firefox reward tables). I’m not suggesting anyone needs to match those exact amounts — that’s for each company to decide — but having clear, consistent expectations about what qualifies as a bug and a transparent patching process would go a long way.
Good changes
On August 4, 2016, Microsoft included design bugs in their Edge bounty [extended until June 30, 2017] (by design bugs I mean SOP bypasses, UXSS, referrer spoofing, etc). The list has room to grow, but it’s a good start. Internet Explorer is still excluded, though. In other words, a researcher who finds a way to access a user’s credentials on IE will be thanked and told it might be patched within 120 days — while the equivalent finding on Edge earns a financial reward.
The business rationale here is understandable — Microsoft is focused on Edge and wants to move users forward — but during that transition there is still a very large IE user base that needs protection, roughly five times the size of Edge’s at the time of writing.
To be clear: I think the move toward Edge is the right direction. A faster and more secure browser benefits everyone. But users don’t disappear overnight just because a vendor stops actively promoting the old product. We need to keep protecting them during the transition, especially because attackers are aware of the numbers too. They actively exploit design bugs like fingerprinting the PC and delivering malware only to users without analyst tools installed.
Browser Market Share 2016 Q3
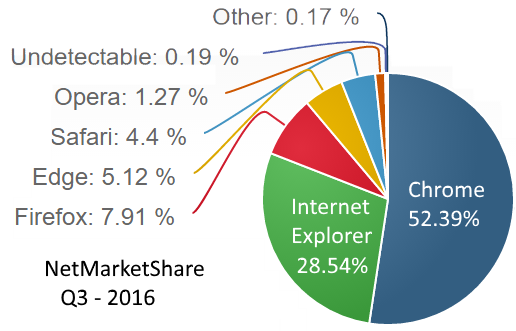
Source: netmarketshare.com
The market share at the time (Q3 2016) shows how large the IE user base still was. Attackers can fingerprint IE users with reasonable precision in order to target their victims, and as long as vulnerable users exist they will be targeted. When a bug is known to be exploited in the wild, it deserves fast-track attention.
Privacy expectations have also risen significantly compared to even five years ago. The ability to fingerprint a user through the browser is now widely recognized as a problem worth fixing, and most browser vendors actively work to prevent it. Aligning on that standard across all supported products would help protect more people.
We need to attract honest, thoughtful bug hunters and give them real motivation to research and report responsibly. That means agreeing on what a bug is, paying fairly for it, and patching promptly. The engine that runs IE, Trident, is still used by several desktop applications — including, at the time, desktop Skype. Supporting those users matters.
Patching Time and Bounties
A 60-day maximum patching window seems fair. Researchers have reported waiting longer than advertised for their findings to be addressed, and the gap between stated and actual timelines erodes trust on both sides.
Bug bounties work best when they stay open for as long as the related products are supported. Closing a program early creates an incentive for researchers to sit on their findings and wait for the next bounty window to open — which helps no one except attackers. Keeping things open and predictable benefits everyone.
The idea that rotating bounties across products drives researchers to switch focus is partially true, but there is also a large group of people who have particular interests and won’t follow the money from one product to another. IE and Edge are exposed every time a user opens a browser, and a single page visit can be enough to trigger a serious vulnerability.
I sincerely hope these ideas are useful to someone on the team. We are ultimately all on the same side here — trying to protect users who often have no idea any of this is happening. A transparent, fast, well-funded security process is one of the best ways to do that.
On full disclosure: I’m generally against it when the affected company is clearly acting in good faith and working hard to fix things. When that trust is established, responsible disclosure makes a lot of sense. I’ll keep sharing what I find, and I hope it helps move things forward.
Respect
My sincere respect to Edge and IE developers. Building a modern, secure browser is genuinely hard, and the work they do matters. What I’d love to see is a permanent team dedicated to attacking design-level assumptions — not just memory safety — because design bugs are still there, and they require a different mindset to find and fix.
Thank you for reading until this point and have a nice day!